Securing Always-On Agents: Keycard Meets OpenClaw

Keycard secures how coding agents access external services - identity, scoped credentials, policy enforcement, audit trails. We’ve been doing this for coding agents like Claude Code, Cursor, and Codex, where the pattern is well understood: a developer runs a tool, the tool needs credentials, Keycard brokers them.
OpenClaw and the ecosystem that sprouted around it made everyone rethink that. These aren’t coding assistants you open and close. They run 24/7. They autonomously manage calendars, query CRMs, push code, monitor infrastructure, run scheduled jobs, hand off work to sub-agents. It’s a different paradigm from what coding agents introduced and it’s forcing a question the whole industry is bumping into: what does identity and access actually look like when agents run on their own?
How OpenClaw Manages Access Today
OpenClaw connects to external services through tool calls: shell commands, API requests, browser automation. It authenticates the way most agent platforms do, by using static API keys and OAuth tokens in environment variables or config files.
That works fine to get started, in the same way it’s “fine” to swim with sharks while carrying a bucket of dolphin meat. But it means the agent holds every key, all the time. There’s no difference between “read the calendar” and “delete all events.” No record of which credentials got used when. If the environment is compromised, everything goes with it.
For a coding agent that runs a few minutes at a time, you can live with that. For something that’s always on with access to production services, you can’t.
Adding Governance Without Breaking the Agent
So the question becomes: how do you layer in credential management and access control without crippling the thing that makes OpenClaw useful?
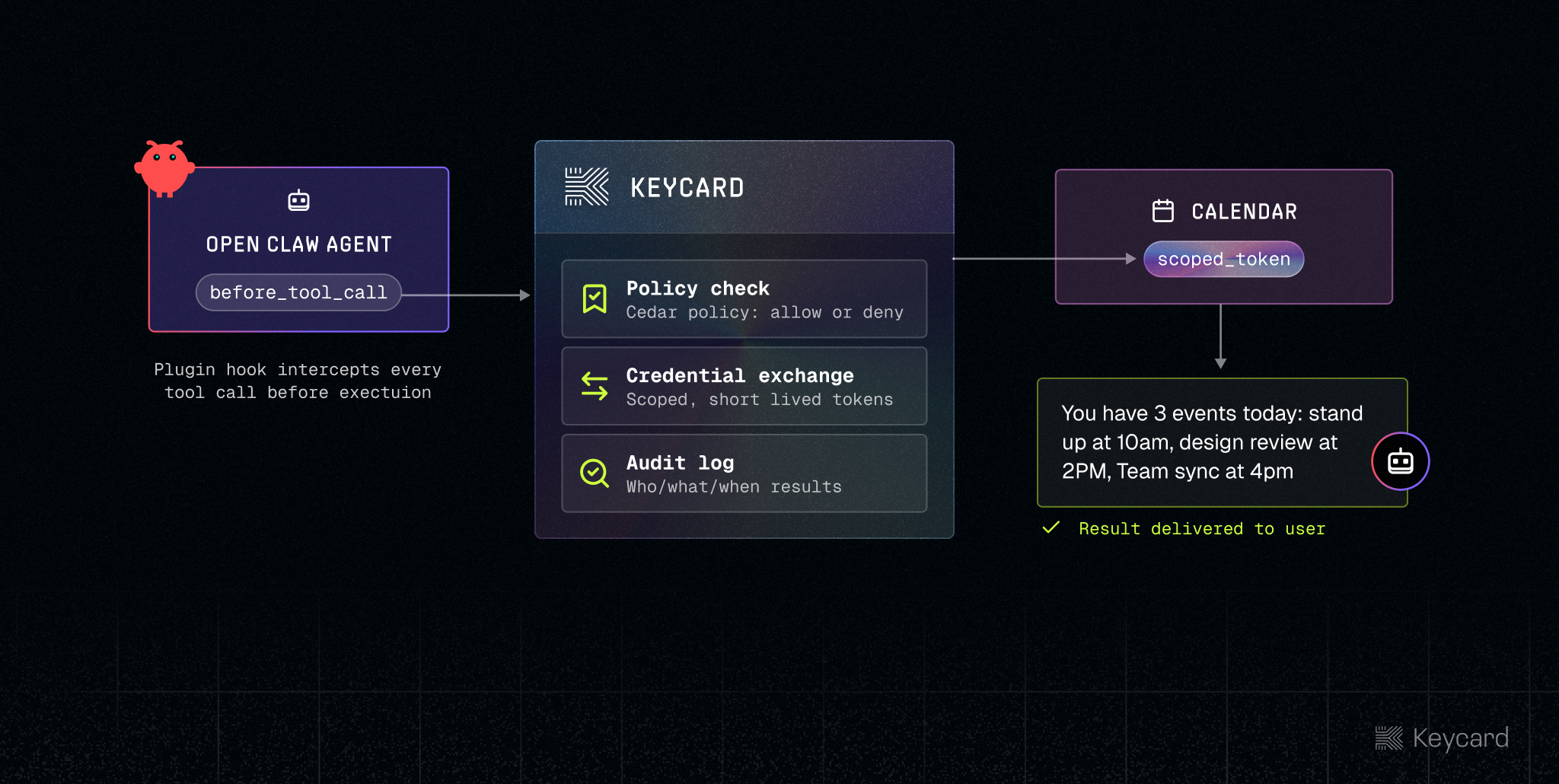
OpenClaw’s plugin system gave us a clean seam. There’s a hook called before_tool_call that fires before every tool the agent uses. Before it runs a command, calls an API, or touches a file. We built a Keycard plugin that sits in that hook and it does two things:
Credentials on demand. Instead of a .env file, the plugin asks Keycard for a token the moment the agent needs one. Keycard checks the request, does an OAuth token exchange, and hands back a credential scoped to that call.
Policy before execution. Every tool call runs through policy first. You can have it set so the agent can read the calendar and create events, but can’t delete them. It can use GitHub but can’t run sudo. If a call gets denied, it doesn’t run. The agent gets a reason and moves on.
The thing we held firm on: the agent itself doesn’t change. It knows credentials are managed for it, it has a skill that tells it not to authenticate itself or store tokens, but it never touches a credential directly. It just uses its tools and Keycard handles the rest.
With these two features, three things happen:
Policy updates are instant. Change a policy rule and the next tool call sees it. No restarts. When you’re figuring out what an agent should and shouldn’t be allowed to do, that tight loop is crucial.
We pulled keys out of the environment. The agent still does everything it did before. GitHub, Google Calendar, search APIs, they all still work. The difference is every request goes through Keycard now. Scoped tokens, short TTLs, everything logged.
You can actually answer “what did the agent do.” Not what it said it did. What actually happened. Every credential exchange and tool call is in Keycard: who requested what, which resource, when, whether it was allowed. That’s the kind of record you need when something goes wrong at 3am and nobody is watching.
What’s Next
OpenClaw pushed the boundaries for our industry. The persistent runtime, the sub-agent delegation, giving it unfettered access to external services and a desktop environment has opened the door to a new reality. But this new reality comes with monsters under the bed and demogorgons in the shadows. It’s clear that these new paradigms are where the industry is headed and we must build the right primitives and patterns to get this right.
We’re building Keycard to handle these architectures as they grow: persistent agents, agents calling other agents, access that crosses org boundaries. The work with OpenClaw is how we’re testing those ideas against reality.
Early Access
If you’re building agents that talk to external services and you’ve hit the limits of static credentials, we should talk!