Announcing Keycard for Coding Agents: Unlocking Autonomy without Sacrificing Security

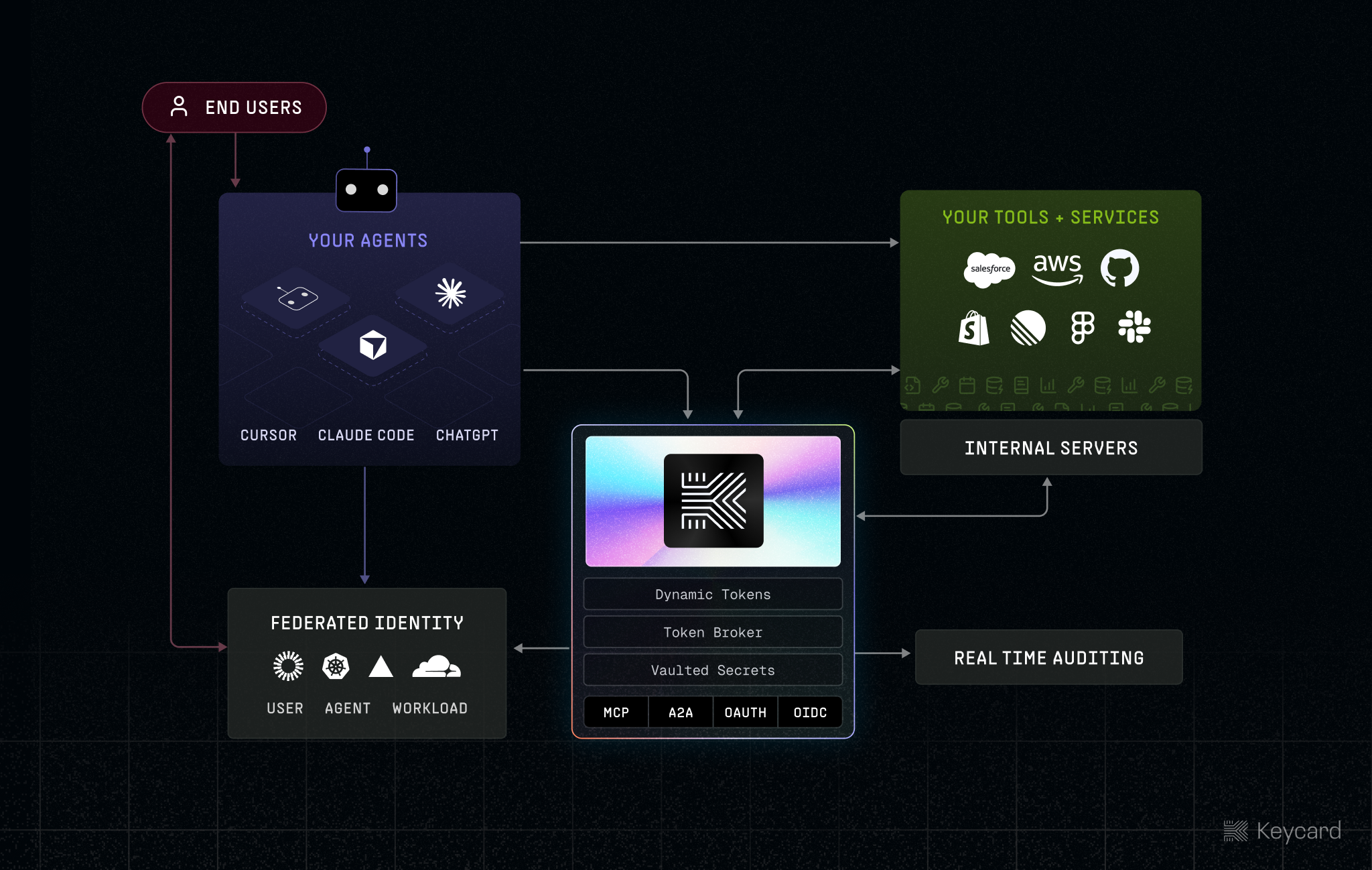
Today, we’re excited to announce Keycard for Coding Agents: identity, access, and governance for Claude Code, OpenAI Codex, OpenCode, Cursor, and any coding agent your team runs or builds across laptops, sandboxes, and CI environments.
Coding agents are eating software development, and with it, software itself. But they’re doing it with borrowed credentials, unintended tool calls, and a control model that forces developers into a bad tradeoff between --dangerously-skip-permissions and constantly approving tool calls.
Keycard fixes this by integrating directly into the coding agent lifecycle through the keycard run command or via our SDKs, ensuring agents only have access scoped to the task, who they’re acting on behalf of, and where they run. It provides a single entry point across developer laptops, sandboxes, and cloud environments, so agents can operate with real autonomy inside a governed boundary without ever having overscoped access.
This eliminates consent fatigue without sacrificing capability. It works with any CLI, API, MCP, sub-agent, or tool an agent creates, and the same primitives are available through our SDKs.
The Problem: Agents Break Traditional Security
Agents don’t just break existing security models, they invalidate the core assumption underneath them. They’re not humans, and they’re not workloads. They reason across many possible paths, operate with evolving context, invoke tools dynamically, and run on non-deterministic models.

If you force them into existing systems, they inherit the wrong thing: human credentials with broad access, or service accounts backed by overscoped API keys. These systems weren’t built for delegated access, so nothing can distinguish between Sara and the agent acting on her behalf. The model assumes a single actor: a human or a workload operating independently.
For developers, it’s death by consent dialog. Every tool call becomes Allow / Deny. You click yes enough times that you stop reading, or you reach for --dangerously-skip-permissions and move on. That flag exists everywhere because everyone knows consent dialogs don’t work—the only alternative today is turning controls off entirely. Clicking “yes” on autopilot isn’t security, it just delays the mistake.
For security, it’s worse. Developers pass around OAuth tokens, static API keys, and .env files just to get things working, with no way to govern or observe what agents are actually doing. Those credentials are massively overscoped. Agents get admin access when they only need read on a single resource, and you can’t express things like “never delete” or “require approval before write,” because the credential and the policy are completely disconnected.
For the organization, it turns into sprawl. Teams aren’t using one agent, they’re using all of them, and building their own. Each one is configured differently across laptops, repos, and cloud environments, with its own permission model and its own way of handling tools and policy. The result is a fragmented, invisible system that’s impossible to control or reason about.
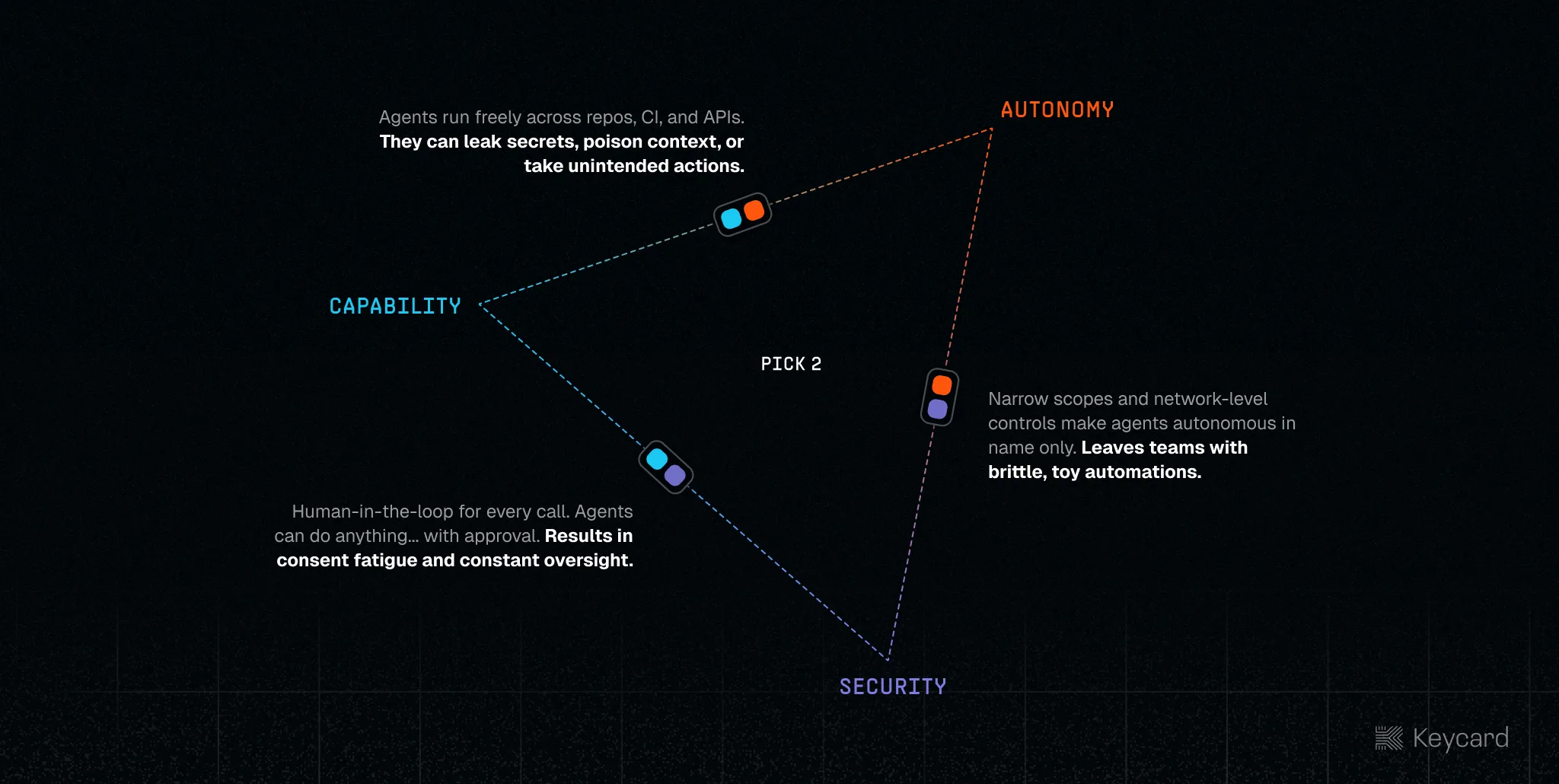
The result is a false choice: pick two of security, autonomy, and capability. Most teams either lock things down and lose the upside, or open them up and accept the risk, so agents never get real authority not because the models aren’t capable, but because there’s no safe way to give them access to what matters.
Introducing Keycard for Coding Agents
Keycard for Coding Agents unifies local tools and upstream services under a single policy layer to authenticate, authorize, and observe every action an agent takes, regardless of where it’s running.
Keycard integrates directly into the agent lifecycle through systems like Claude Code and Cursor’s hook and tool approval APIs, intercepting prompts and tool calls at the execution boundary and evaluating them before they run. Each action is issued credentials scoped to the task, agent, user, and environment, with telemetry captured in real time alongside full identity context.

By resolving who is delegating (the user), who is acting (the agent), where it’s running (the device), and what it’s trying to do (the task) in the context of a session, Keycard can evaluate intent and provide end to end governance. This model not only enables true delegated access, it also enables delegation chaining, ensuring every sub-agent or tool call cannot exceed the privileges of the parent.
Because Keycard supports device and workload attestations, it can establish this identity directly from the environment the agent runs in without relying on long-lived credentials or pre-provisioned secrets and without needing to copy credentials into .env files, meaning agents never have direct access to long-lived secrets. This makes it possible to define how agents operate once and have it apply everywhere, with policy, credentials, and auditing expressed in a single model.
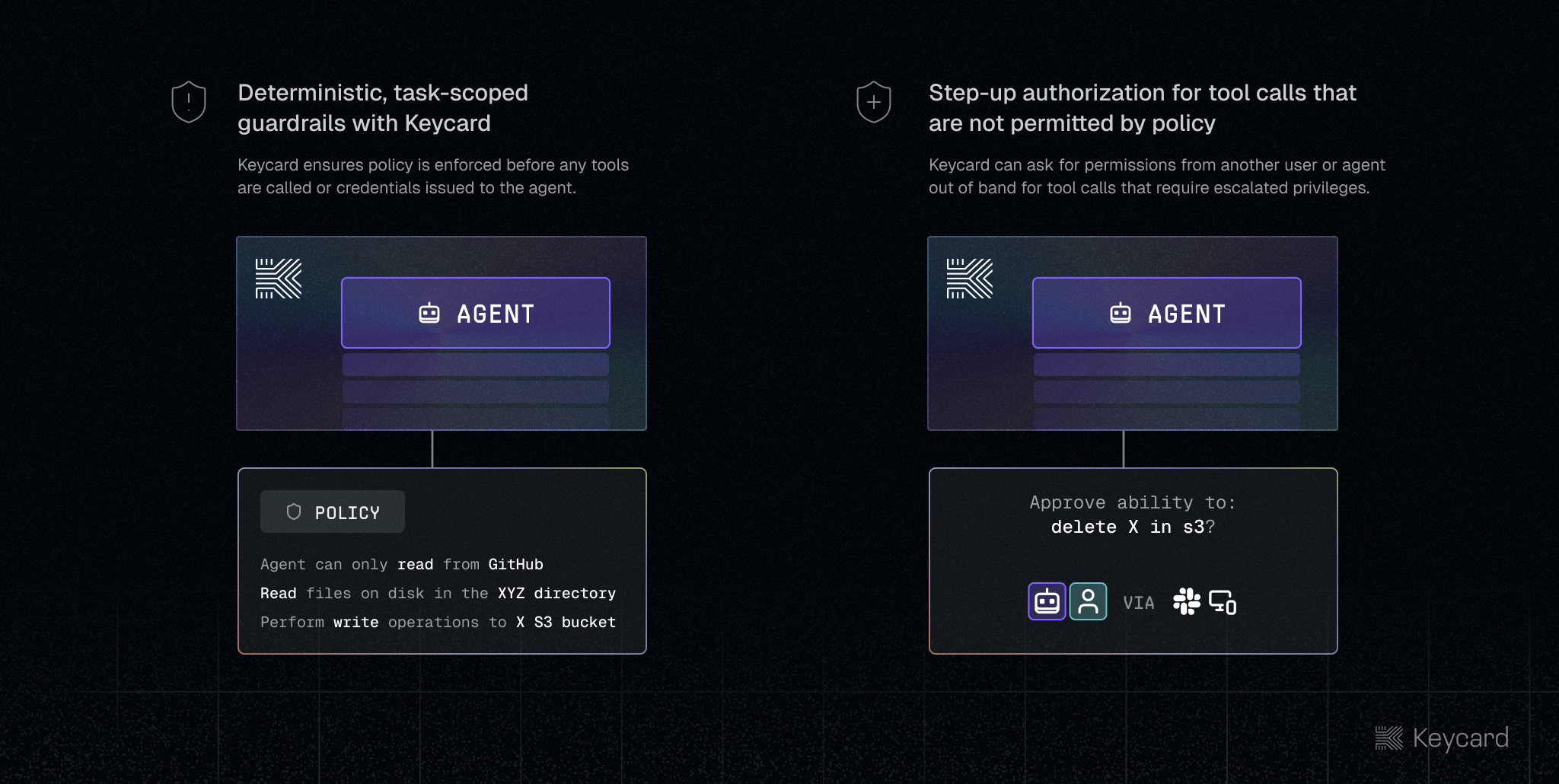
At runtime, tool calls are evaluated inline and credentials are injected just-in-time for that specific action and identity, allowing agents to operate autonomously within those boundaries, while actions that cross a threshold such as accessing sensitive data, modifying critical systems, or performing destructive operations, trigger step-up authorization tied to that exact context.
In practice, Sara is still Sara, and Claude Code is still Claude Code running on her laptop, but her agent no longer inherits her access, instead receiving credentials scoped to the task. Sara still has read and write access to the Postgres database, while her agent is limited to reading specific tables as defined by centralized, application-, agent-, and repository-level policy.
For organizations that want stronger guarantees, Keycard can also be deployed with a gateway that ensures agents never have access to real credentials. The gateway can run on-device, in your cloud, alongside a sandbox, or on Keycard’s infrastructure, and is built on the same SDKs that power Keycard for Coding Agents.
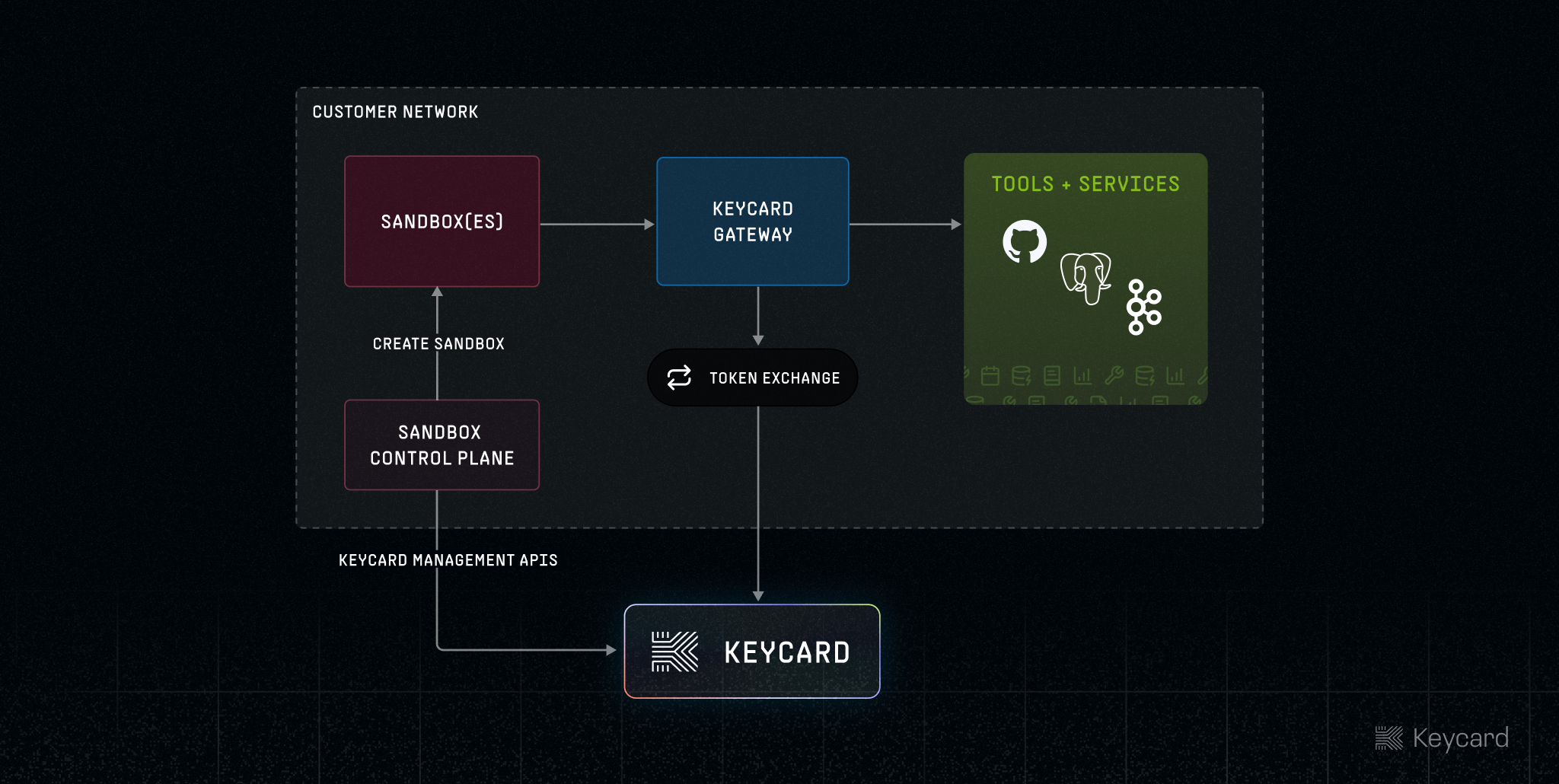
Agents are issued opaque device- and identity-attested credentials scoped to the session and resource, which are exchanged at the boundary for real credentials per tool call, ensuring credentials are never exposed to the agent, never written to disk, and never reusable outside the context they were issued for.
Powered by the Keycard Platform
Under the hood, Keycard for Code is built on the Keycard Platform, which models the relationships between applications, agents, users, sessions, workloads, and devices, and uses that context to derive identity, access, and control across everything an agent touches.
Most systems treat identity and access as something configured ahead of time, but that model breaks down with agents. Keycard evaluates identity and access at execution time using the full context of who initiated the action, which agent is acting, where it’s running, and what it’s trying to do.
The same primitives that power keycard run are exposed through the Keycard SDKs, so anything you build inherits this model by default. Whether you’re working with MCP, A2A, or any presentation-layer protocol (e.g. HTTP, Postgres, etc), Keycard handles identity and access for you.
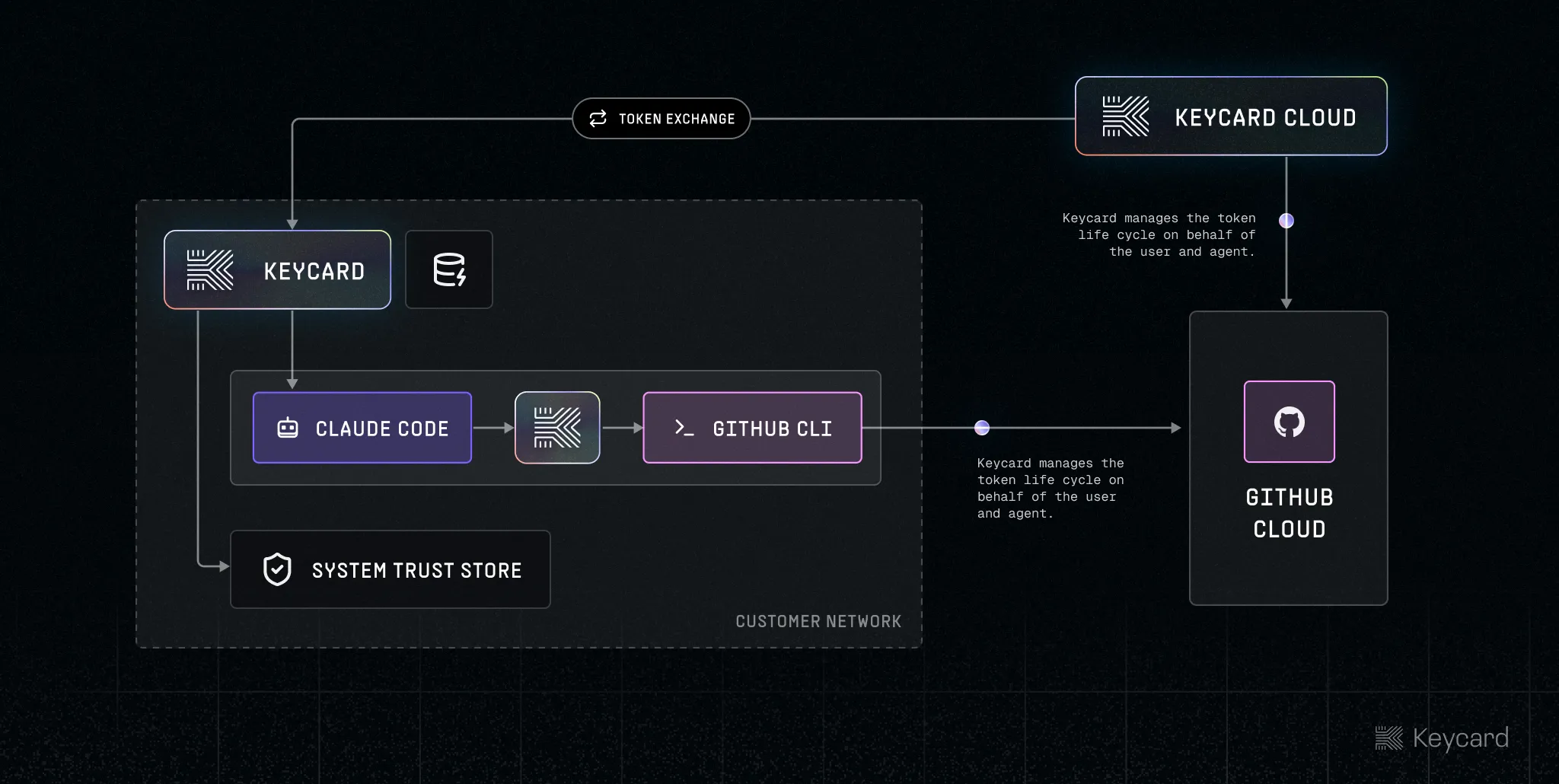
Keycard doesn’t replace the identity systems you already use, it orchestrates them. Built on standards like OAuth 2.1, OIDC, and emerging workload identity protocols, it allows agents to interact with both modern and legacy systems without custom integration. Instead of forcing developers to understand how each system handles delegation, credential exchange, or token lifecycles, Keycard abstracts that complexity behind a single domain model while remaining fully compatible with the protocols those systems expect.
Keycard supports multiple access patterns depending on the system it’s integrating with:
- Federated: for systems that natively support delegation
- Brokered: credentials are issued with appropriate scope attenuation at runtime
- Secrets: static secrets are securely stored, injected, and rotated via a single API call
In all cases, credentials are provisioned and issued based on the accessors identity and runtime context at execution time.
Every action an agent takes is captured as real-time telemetry with full identity context, and because Keycard sits in the execution path, that telemetry is directly tied to control: access can be revoked immediately, policies can be updated in response to live behavior, and those changes propagate across every agent and environment without redeploying anything. Telemetry can also be streamed into existing SIEM systems for real-time detection and response.
Get Early Access Today
Keycard for Coding Agents is available in early access today. We’ve been building and iterating on this platform over the past year, and it’s already in production with customers like Chime.
“We wanted our engineers deploying agents and tools into production without needing to be security or identity experts. Keycard’s platform made that possible. We had agents running against production systems in days.”
— Dennis Yang, Principal Product Manager for Generative AI at Chime
Stop making impossible trade-offs between autonomy, capability and security. You can have it all.